The phrase Internet of Things sounds abstract until you realize how many of the objects around you are already part of it. The thermostat that learns your schedule and adjusts before you wake up. The fitness tracker measuring your heart rate.
The shipping container broadcasting its GPS coordinates across an ocean. The sensor on a factory turbine blade measuring vibration patterns to predict when it will need replacement. All of these are IoT devices — physical objects with the ability to sense their environment and communicate that data over a network.
The term was coined by British technologist Kevin Ashton in 1999, when he was working at Procter and Gamble and used it to describe a system in which everyday objects were connected to the internet via RFID tags, allowing supply chains to be tracked automatically. Since then, the concept has expanded from a vision into a global infrastructure.
By 2024, estimates from IoT Analytics placed the number of connected IoT devices worldwide at over 16 billion, with projections reaching 25 billion by 2030.
The scale of that number deserves a moment of reflection. 16 billion devices is roughly two devices for every human being on earth. Most of those devices are not smartphones or laptops — they are purpose-built sensors and actuators embedded in infrastructure, industry, agriculture, vehicles, and homes, quietly collecting data and executing instructions at a scale that was technically impossible a decade ago and economically impossible two decades ago.
This article explains what IoT is, how it works technically, where it is being applied, what its risks are, and why it matters for businesses and individuals alike.
What Makes Something an IoT Device
Not every internet-connected device qualifies as IoT. A laptop or smartphone is a general-purpose computing device. An IoT device is typically a purpose-built physical object — a sensor, an actuator, or a combination — that collects specific data from its environment or performs a specific physical action, usually with limited local processing capability.
The key characteristics of IoT devices are:
- Sensing or actuation: they measure something (temperature, motion, light, pressure, location) or control something (a valve, a light, a motor)
- Connectivity: they transmit data to or receive instructions from a network
- Embedded intelligence: they contain a microprocessor or microcontroller running firmware that manages operation and communication
- Often autonomous operation: they run continuously without regular human interaction
- Purpose-specific design: they are built to do one thing well rather than general-purpose computing
The diversity of IoT devices is enormous. A soil moisture sensor in an agricultural field, a pacemaker transmitting cardiac data to a hospital, a smart meter reporting electricity consumption every fifteen minutes, and a connected industrial robot arm are all IoT devices — despite having almost nothing in common in terms of form factor, application, or scale.
The Enabling Technologies
Three converging technological trends have made the current scale of IoT deployment economically feasible.
Falling sensor costs: The price of sensors has fallen dramatically over the past two decades. A MEMS (microelectromechanical systems) accelerometer that cost several dollars in 2000 costs fractions of a cent today. This cost trajectory has made embedding sensors in objects that previously could not justify the expense — packaging, clothing, agricultural equipment — economically viable.
Low-power wireless connectivity: The development of protocols specifically designed for power-constrained devices — Bluetooth Low Energy, Zigbee, LoRaWAN, NB-IoT — has made battery-powered deployment practical for applications where wired connectivity is impossible and where battery replacement must be minimized. Some agricultural sensors now operate for five to ten years on a single battery.
Cloud computing: The availability of scalable, affordable cloud infrastructure has removed the requirement to build and maintain on-premise server capacity proportional to the IoT deployment. Organizations can start collecting data from a handful of sensors and scale to millions without upfront infrastructure investment.
How IoT Works: The Four-Layer Architecture
A useful way to understand IoT technically is through its architecture, which typically spans four interconnected layers.
Layer 1: Devices (Sensors and Actuators)
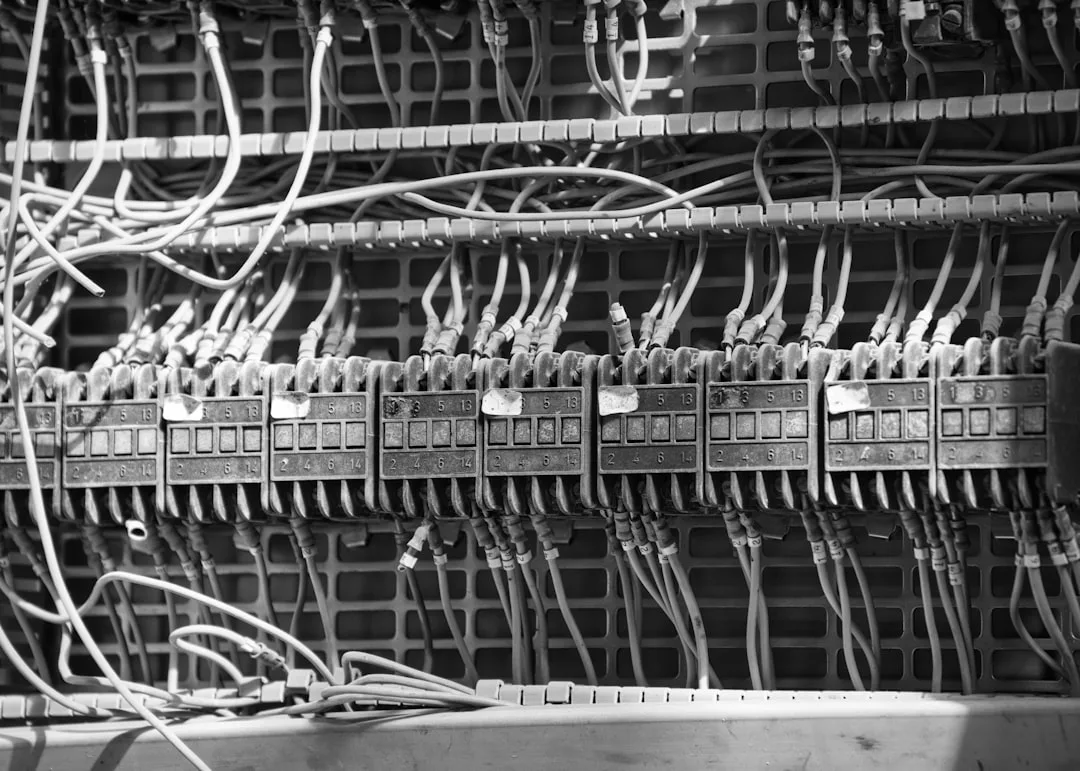
At the foundation are the physical devices themselves. Sensors convert physical phenomena — temperature, humidity, acceleration, light, sound, chemical composition, location — into electronic signals. Actuators work in the opposite direction: they convert electronic signals into physical actions, such as opening a valve, activating a motor, or switching a light.
Modern IoT devices typically include a microcontroller (a small, low-power processor), one or more sensors or actuators, a communication module, and a power source (battery, wired power, or energy harvesting). The trend toward system-on-chip (SoC) designs has consolidated these components, reducing the size and cost of capable IoT devices to the point where they can be embedded in almost any physical object.
Edge AI chips — small, low-power processors specifically designed to run machine learning inference at the device level — represent the current frontier of IoT device hardware. Products like the Arm Ethos series and Google's Edge TPU allow IoT devices to run computer vision models, anomaly detection, and classification tasks locally, without sending raw data to the cloud. This capability is transforming what IoT devices can do independently.
Layer 2: Connectivity
The connectivity layer is responsible for transmitting data from devices to processing systems. The appropriate protocol depends on factors including the required range, the data volume, the power availability, and the cost constraints of the deployment.
| Protocol | Range | Power Use | Typical Data Rate | Best For |
|---|---|---|---|---|
| Wi-Fi (802.11) | Medium (tens of meters) | High | Up to 600 Mbps | Home devices, fixed industrial sensors |
| Bluetooth / BLE | Short (10-100m) | Very low | 1-3 Mbps | Wearables, proximity sensors, asset tags |
| Zigbee / Z-Wave | Short to medium | Low | 250 kbps | Smart home mesh networks |
| LoRaWAN | Long (1-15km) | Very low | 0.3-50 kbps | Agricultural, smart city, remote monitoring |
| Cellular (4G/5G) | Wide (cellular coverage) | Medium-high | Up to Gbps (5G) | Vehicles, mobile assets, remote deployments |
| NB-IoT / LTE-M | Wide | Low | 200 kbps | Low-bandwidth static sensors |
| Thread / Matter | Short to medium | Low | 250 kbps | Smart home (new standard) |
MQTT (Message Queuing Telemetry Transport) and CoAP (Constrained Application Protocol) are the dominant messaging protocols for IoT communication. Both were designed with resource-constrained devices in mind.
MQTT uses a publish-subscribe model: devices publish data to a central broker, and applications subscribe to receive that data. It is efficient, handles unreliable connections gracefully, and is widely supported across all major cloud IoT platforms. CoAP is a RESTful protocol designed for devices too constrained to run HTTP, offering similar request-response semantics with far lower overhead.
The 5G rollout is creating new IoT deployment possibilities that 4G could not support economically. 5G's massive machine-type communications (mMTC) capability is specifically designed for high-density IoT: urban environments where thousands of sensors per square kilometer need to coexist. The combination of 5G density, low-latency, and network slicing (dedicating bandwidth segments to specific use cases) will make applications like real-time smart city infrastructure management and autonomous vehicle coordination practically achievable at scale.
Layer 3: Processing
Once data leaves the device, it needs to be processed. This can happen at three points:
Cloud processing sends raw data to centralized servers for analysis, storage, and application logic. Cloud platforms from AWS (IoT Core), Microsoft (Azure IoT Hub), and Google (Cloud IoT) provide managed infrastructure for large-scale IoT deployments. Cloud processing is appropriate for applications where latency is not critical (reporting, analytics, historical trends) and where data from many distributed devices needs to be aggregated and compared.
Edge computing processes data at or near the device, reducing latency and bandwidth consumption. An edge gateway in a factory might aggregate and analyze data from dozens of sensors locally, sending only anomalies or summaries to the cloud rather than raw streams. This is critical for applications requiring millisecond response times, such as automated quality control on a manufacturing line or vehicle collision avoidance.
Fog computing refers to processing infrastructure distributed between the device and the cloud — local servers or network gateways that handle intermediate processing. The term is used inconsistently across the industry; many organizations simply use "edge computing" as an umbrella term for any processing that occurs closer to the device than the central cloud.
The edge versus cloud decision is increasingly nuanced. Sending all raw sensor data to the cloud is bandwidth-intensive and creates latency. Processing everything at the edge requires more capable (and expensive) edge hardware. Modern architectures typically use a hybrid: edge devices handle real-time reaction and preprocessing, while the cloud handles long-term storage, cross-device analytics, and model training.
Layer 4: Applications
The application layer is where IoT data becomes useful to humans or automated systems. Applications might include a dashboard showing real-time energy consumption across a building portfolio, an alert when a patient's monitored vital signs fall outside normal ranges, an automated reorder trigger when inventory sensors detect low stock, or a maintenance ticket generated when a machine's vibration signature indicates bearing wear.
Application integration is often the most complex part of IoT deployment — not because connecting sensors is hard, but because making the resulting data actionable within existing business systems (ERP, CRM, SCADA, EHR) requires significant integration work. The sensors produce data; turning data into business value requires connecting it to the workflows, decisions, and systems that shape how an organization operates.
Consumer IoT: The Smart Home and Beyond
Consumer IoT has driven public awareness of the technology. The smart home category includes connected thermostats (Nest, Ecobee), smart speakers (Amazon Echo, Google Home), connected lighting (Philips Hue, LIFX), smart locks, video doorbells, security cameras, and kitchen appliances.
The appeal is convenience and energy efficiency. A smart thermostat can reduce heating and cooling costs by learning occupancy patterns and responding to weather forecasts. Smart lighting can adjust automatically to time of day and occupancy. Connected appliances can notify owners of unusual conditions — a refrigerator reporting a door left open, a washing machine signaling a completed cycle.
According to the U.S. Energy Information Administration, smart thermostats and energy management systems have demonstrated average energy savings of 8-15% on heating and cooling costs in residential settings where they replace basic programmable thermostats.
The smart home ecosystem faced a fragmentation problem for years: devices from different manufacturers did not communicate with each other, requiring separate apps and incompatible hubs. The Matter standard, developed by the Connectivity Standards Alliance (formerly the Zigbee Alliance) with backing from Apple, Google, Amazon, and Samsung, is designed to resolve this.
Matter-certified devices can interoperate across different manufacturers' ecosystems and voice assistants, which industry analysts expect to significantly accelerate consumer IoT adoption as it reaches broad market penetration.
Beyond the home, consumer IoT extends to:
Wearables: Fitness trackers, smartwatches, continuous glucose monitors (CGMs), and smart inhalers. CGMs have been particularly transformative for diabetes management — they remove the need for finger-prick blood tests by providing continuous glucose readings transmitted to a smartphone, enabling more precise insulin dosing and alerting patients and caregivers to dangerous glucose trends in real time.
Connected vehicles: Modern vehicles contain dozens to hundreds of sensors communicating over internal networks, with telematics systems transmitting diagnostic data, location, and driving behavior. Over-the-air (OTA) software updates — pioneered by Tesla and now adopted broadly — treat vehicles as IoT devices that improve over their lifetime rather than degrading.
Personal health monitoring: The convergence of consumer wearables with clinical-grade sensors is enabling continuous health monitoring outside clinical settings. Consumer ECG monitors, blood oxygen sensors, and stress indicators are generating health data at a scale that was previously available only in intensive care settings. The clinical validity and privacy implications of this data are active areas of medical and regulatory debate.
Industrial IoT: Where Scale and Stakes Are Highest
Industrial IoT (IIoT) applies connected sensing and automation to manufacturing, logistics, energy, agriculture, and critical infrastructure. The scale is enormous and the applications are high-stakes.
Predictive Maintenance
One of IIoT's most valuable applications is predictive maintenance — using sensor data to anticipate equipment failures before they occur. Vibration sensors on rotating machinery, thermal cameras monitoring electrical switchgear, and acoustic sensors detecting abnormal sounds from compressors can all provide early warning of developing faults.
The economics are compelling. Unplanned downtime in manufacturing can cost thousands to tens of thousands of dollars per minute depending on the industry. McKinsey estimated in 2020 that predictive maintenance enabled by IIoT can reduce maintenance costs by 10-25% and unplanned downtime by 50%. In capital-intensive industries like oil and gas, mining, and aviation, these reductions represent hundreds of millions of dollars annually for large operators.
General Electric's Predix platform is the most cited enterprise example of IIoT-enabled predictive maintenance at scale. GE equipped its aviation and power generation equipment with thousands of sensors per asset and built analytics models to detect anomalies indicating developing failures weeks before they would cause operational problems. The company estimated this capability prevented over 1,000 equipment failures in its aviation business alone.
Supply Chain and Logistics
IoT tracking devices on shipments, containers, and vehicles provide real-time visibility across global supply chains. Condition monitoring sensors (temperature, humidity, shock) on pharmaceutical shipments or food products can document handling conditions throughout the cold chain and trigger alerts if conditions fall outside specifications.
Maersk, the world's largest container shipping company, has deployed IoT-connected containers ("remote container management") across hundreds of thousands of refrigerated containers. Sensors monitor temperature, humidity, and CO2 levels every fifteen minutes, with automated alerts sent to operations staff and customers when conditions deviate.
The system reduces spoilage losses and provides the documentation required for food safety compliance across global supply chains.
Smart Agriculture
Agricultural IoT — sometimes called precision agriculture or AgriTech — uses soil sensors, weather stations, drone-mounted cameras, and automated irrigation systems to optimize resource use. Soil moisture sensors can reduce irrigation water use by 20-50% in some crops by ensuring water is applied only when and where needed.
John Deere's Operations Center platform aggregates data from GPS-equipped equipment, yield monitors, soil sensors, and weather stations to provide farm-level analytics that inform planting, application, and harvesting decisions. The platform now connects over 300 million acres of farmland globally. As climate variability increases agricultural risk, the value of data-driven resource optimization rises proportionately.
Smart Cities
Urban IoT applications include smart traffic management (adjusting signal timing based on real-time flow), environmental monitoring (air quality, noise levels), smart parking (guiding drivers to available spaces), and connected public lighting (dimming when streets are empty to save energy).
Barcelona is frequently cited as an early leader in smart city IoT deployment. The city deployed a network of sensors in parks, roads, and public facilities that reduced water use for irrigation by 25%, reduced parking search times (and the emissions they generate) through smart parking guidance, and enabled real-time environmental monitoring across neighborhoods. The city estimates combined annual savings exceeding 42 million euros from its smart city program.
Singapore's Smart Nation initiative represents the most comprehensive national-scale smart city program. It encompasses sensors for traffic management, public safety, utility monitoring, and urban planning research, with data flowing into a city-state-scale digital twin that informs infrastructure planning and operational optimization.
IoT Security: The Uncomfortable Reality
IoT security is one of the technology's most serious and underaddressed challenges. The attack surface created by billions of connected devices is vast, and many of those devices are poorly secured.
The Core Problems
Default credentials: Many IoT devices ship with default usernames and passwords (often "admin/admin" or similar) that most consumers never change. These credentials are publicly documented and trivially exploited.
Infrequent updates: Unlike smartphones, which receive regular security updates, many IoT devices are never updated after deployment. Vulnerabilities discovered years after a product ships may remain unpatched indefinitely because the manufacturer has no update mechanism, has end-of-lifed the product, or the user has no way to apply updates.
Limited processing resources: Encryption and authentication require processing power and memory. Resource-constrained devices sometimes implement weak or no encryption to preserve battery life and processing capacity.
Network exposure: Many IoT devices are exposed directly to the internet or placed on networks with insufficient segmentation, making them accessible to attackers who can then use them to pivot to more sensitive systems.
Long deployment lifespans: A consumer refrigerator or building management sensor may be deployed for 10-20 years. Security assumptions valid at deployment often become dangerously outdated long before the device is retired.
Notable Incidents
The Mirai botnet of 2016 demonstrated the consequences at scale. Malware scanned the internet for IoT devices using default credentials, compromised hundreds of thousands of cameras and routers, and recruited them into a botnet that launched what were at the time among the largest distributed denial-of-service (DDoS) attacks ever recorded, temporarily disrupting major services including Twitter, Reddit, Netflix, and Spotify.
The Mirai source code was subsequently released publicly, spawning dozens of derivative botnets.
In 2021, a threat actor accessed the control systems of the Oldsmar, Florida water treatment plant through a remote access tool running on an operational technology network, and briefly attempted to change the sodium hydroxide (lye) concentration to dangerous levels. An operator noticed the change and reversed it in real time.
The incident illustrated that ICS/SCADA systems — industrial control systems that include IoT components — can have directly life-threatening security implications.
In healthcare, IoT security failures have directly threatened patient safety. The FDA has issued numerous warnings about vulnerabilities in connected medical devices including infusion pumps, cardiac monitors, and insulin delivery systems. In 2019, Medtronic recalled nearly half a million implantable cardioverter-defibrillators due to cybersecurity vulnerabilities that could potentially allow unauthorized remote access.
The Regulatory Response
Regulators are beginning to address IoT security through legislation and standards requirements.
The UK's Product Security and Telecommunications Infrastructure Act (2022) bans default passwords on consumer IoT devices, requires manufacturers to publish vulnerability disclosure policies, and requires transparency about the minimum period of security updates.
The EU's Cyber Resilience Act (2024) imposes mandatory cybersecurity requirements on products with digital elements sold in Europe, including IoT devices, with CE marking dependent on meeting security requirements.
In the United States, the NIST Cybersecurity Framework and NIST IR 8259 series provide IoT security guidance that is increasingly referenced in federal procurement requirements, creating market pressure on vendors even without direct regulation.
Improving IoT Security
Best practices for IoT security include:
- Changing default credentials immediately on deployment
- Placing IoT devices on segregated network segments, separate from computers and sensitive systems
- Disabling unused features, ports, and protocols
- Applying firmware updates promptly when available
- Selecting vendors with clear security update policies and defined support periods
- Using network monitoring to detect anomalous device behavior
For organizations deploying IoT at scale, security by design — evaluating security requirements before device selection and procurement — is far more effective than attempting to secure poorly designed devices after deployment. Including security requirements in vendor RFPs, requiring evidence of security testing, and mandating update support periods are procurement-level controls that shape the security posture of an entire deployment before the first device is installed.
IoT Market Size and Growth
IoT is one of the fastest-growing technology sectors. Key market figures:
| Metric | Figure | Source / Year |
|---|---|---|
| Global connected IoT devices | 16.6 billion | IoT Analytics, 2024 |
| Projected devices by 2030 | 25+ billion | IoT Analytics, 2024 |
| Global IoT market revenue | ~$805 billion | Fortune Business Insights, 2023 |
| Projected market size 2030 | ~$2.5 trillion | Multiple analyst consensus |
| Industrial IoT market share | ~35% of total | McKinsey Global Institute |
| IoT semiconductor market | $65 billion | Semiconductor Industry Association, 2023 |
Growth is driven by declining sensor and connectivity costs, the expansion of 5G networks (which enable higher-density IoT deployments), and the accumulating business case from predictive maintenance, supply chain optimization, and energy management applications.
The industrial segment is growing fastest in absolute terms. As organizations move from pilot deployments to enterprise-scale rollouts, and as cloud platforms mature their IoT infrastructure offerings, the conversion rate from IoT interest to active deployment is increasing.
Key Challenges Holding IoT Back
Despite its growth, IoT adoption faces several structural challenges:
Interoperability: The IoT ecosystem is fragmented across incompatible standards, protocols, and platforms. A Zigbee device may not communicate with a Z-Wave hub; a sensor designed for one cloud platform may not integrate cleanly with another. The Matter standard is making progress in consumer IoT, but industrial IoT fragmentation remains severe.
Organizations building complex IIoT deployments often face a long-tail integration problem: most of the major equipment vendors are connected, but the 20% of devices from smaller vendors require custom integration work that is disproportionately expensive.
Data management: Large IoT deployments generate enormous volumes of data. A single wind turbine with comprehensive sensing produces terabytes of data per year. Deciding what to store, how long to retain it, how to compress it without losing analytical value, and how to extract actionable insight from it requires significant data engineering capability that many organizations lack.
Privacy: Consumer IoT devices continuously collect behavioral data. Smart speakers capture audio fragments, cameras capture movement and faces, fitness trackers capture biometric data continuously, and location tracking on connected vehicles builds detailed records of physical movements. The privacy implications of this persistent data collection remain underregulated in many jurisdictions and poorly understood by most consumers who accept terms of service without reading them.
The EU's General Data Protection Regulation (GDPR) and California's CCPA apply to IoT data collection, but enforcement has been inconsistent and consumer awareness remains low. Academic researchers at Carnegie Mellon University have documented that many consumer IoT devices communicate with dozens of third-party data collection endpoints without user awareness.
Total cost of ownership: IoT projects often underestimate the full costs of connectivity, maintenance, data management, and integration. Projects that deliver compelling ROI at small scale sometimes struggle to justify costs at full enterprise deployment when infrastructure overhead, data management costs, and ongoing maintenance are properly accounted for.
The Convergence of IoT, AI, and Edge Computing
The most significant evolution in IoT is the convergence with artificial intelligence and edge computing. Traditional IoT deployments sent raw data to the cloud for analysis; increasingly, intelligence is being deployed at the edge — on the device or at a local gateway — enabling real-time decision-making without cloud round trips.
A camera with on-device AI can identify defective products on a manufacturing line in milliseconds, without sending video to the cloud. A wind turbine controller can adjust blade pitch in response to changing wind conditions faster than a cloud-based system could respond. An agricultural drone can identify diseased plants while flying over a field without a cellular connection.
TensorFlow Lite, PyTorch Mobile, and purpose-built edge AI frameworks from Arm, Intel, and NVIDIA are making it increasingly straightforward to deploy machine learning models on constrained IoT hardware. The combination of better edge hardware, better frameworks, and better model compression techniques is compressing the gap between what AI can do in the cloud and what it can do at the edge.
This convergence of IoT, AI, and edge computing is sometimes called AIoT or the intelligent edge, and it represents the direction of the most sophisticated IoT applications. As edge AI chips become more capable and affordable, the gap between what can be done at the edge and what requires the cloud will continue to narrow.
Digital Twins: IoT's Most Ambitious Application
A digital twin is a virtual model of a physical asset, process, or system that is continuously updated with real-time data from IoT sensors. The virtual model mirrors the state of the physical asset and can be used to simulate scenarios, predict outcomes, and test interventions before implementing them in the physical world.
Siemens, GE, Microsoft, and Ansys are among the major vendors offering digital twin platforms. Applications range from individual machines (a digital twin of a specific jet engine, continuously updated with flight data) to entire facilities (a digital twin of a manufacturing plant, used to optimize production scheduling) to city-scale infrastructure (digital twins used by Singapore and Helsinki for urban planning).
The value proposition is compelling: instead of testing a process change on a physical production line — which interrupts operations and risks quality — engineers test it on the digital twin first. The digital twin simulates the outcome with high fidelity because it is continuously calibrated against real sensor data from the physical asset. This capability represents IoT data being transformed from a reporting tool into a design and decision tool.
Summary
The Internet of Things is the network of physical devices embedded with sensors and connectivity that enables them to collect and exchange data. It spans everything from consumer smart home devices to industrial sensors monitoring critical infrastructure. Its four-layer architecture — devices, connectivity, processing, and applications — provides a framework for understanding how the technology works and where the engineering challenges lie.
IoT's transformative potential lies in its ability to make the physical world legible to software systems: to turn the behavior of machines, environments, and physical processes into data that can be analyzed, acted upon, and optimized. Its risks lie in the security vulnerabilities created by billions of often-poorly-secured connected devices and the privacy implications of persistent data collection.
The organizations and societies that navigate IoT's challenges thoughtfully — investing in security, interoperability, and data governance alongside technical deployment — will capture the productivity and efficiency gains the technology genuinely offers. Those that deploy it carelessly will contribute to an expanding attack surface with consequences that extend far beyond the IoT devices themselves.
References
- IoT Analytics. (2024). State of IoT: Number of Connected IoT Devices Growing. iot-analytics.com
- Fortune Business Insights. (2023). Internet of Things Market Size, Share and Growth Report. fortunebusinessinsights.com
- McKinsey Global Institute. (2020). The Internet of Things: Catching Up to an Accelerating Opportunity. McKinsey and Company.
- Connectivity Standards Alliance. (2024). Matter Smart Home Standard Overview. csa-iot.org
- U.S. Energy Information Administration. (2022). Smart Thermostats: Energy Savings and Market Trends. eia.gov
- National Institute of Standards and Technology. (2022). NIST IR 8259: Foundational Cybersecurity Activities for IoT Device Manufacturers. nist.gov
- European Parliament. (2024). Cyber Resilience Act. europarl.europa.eu
- Krebs, B. (2016). KrebsOnSecurity.com: Mirai Botnet Analysis. krebsonsecurity.com
- FDA. (2022). Medical Device Cybersecurity: Guidance for Industry. fda.gov
- Maersk. (2023). Remote Container Management Platform. maersk.com
- GE Digital. (2022). Predix Platform: Industrial IoT Case Studies. ge.com/digital
- Siemens. (2023). Digital Twin Technology Overview. siemens.com
- Carnegie Mellon University. (2020). IoT Inspector: Measuring Privacy Practices in Smart Home Devices. iot-inspector.com
- Semiconductor Industry Association. (2023). Semiconductor Industry Data and Analysis. semiconductors.org
- World Economic Forum. (2023). The Global Risks Report 2023: Technology Risks. weforum.org
Frequently Asked Questions
What is the Internet of Things (IoT)?
The Internet of Things (IoT) refers to the network of physical devices, vehicles, appliances, and other objects embedded with sensors, software, and connectivity that enables them to collect and exchange data over the internet. IoT devices range from consumer smart speakers and thermostats to industrial sensors monitoring factory equipment and agricultural soil conditions.
How does IoT work technically?
IoT systems consist of four layers: devices (sensors and actuators that gather or act on data), connectivity (protocols like Wi-Fi, Bluetooth, Zigbee, LoRaWAN, or cellular that transmit data), a processing layer (cloud platforms or edge computing nodes that analyze data), and an application layer (software interfaces that present insights or trigger actions). The specific combination of these layers depends on the use case, data volume, and latency requirements.
What are MQTT and CoAP in IoT?
MQTT (Message Queuing Telemetry Transport) is a lightweight publish-subscribe messaging protocol designed for devices with limited processing power and unreliable network connections. CoAP (Constrained Application Protocol) is a specialized web transfer protocol for use with constrained nodes and networks in IoT environments. Both were designed to minimize bandwidth and energy use compared to standard HTTP, making them suited for IoT devices that run on batteries or cellular connections.
What are the main security risks of IoT devices?
IoT devices are frequently deployed with default or weak passwords, outdated firmware, and limited encryption, making them common targets for compromise. Once infected, they can be recruited into botnets (such as the Mirai botnet of 2016, which compromised hundreds of thousands of IoT devices for DDoS attacks), used for network intrusion, or exploited for data theft. The challenge is that many IoT devices have no practical mechanism for user-initiated security updates.
What is the difference between consumer IoT and industrial IoT?
Consumer IoT includes smart home devices such as thermostats, cameras, lights, locks, and voice assistants, where the primary goals are convenience and energy efficiency. Industrial IoT (IIoT) applies connected sensors and automation to manufacturing, logistics, agriculture, and critical infrastructure, where the primary goals are efficiency, predictive maintenance, and safety. IIoT deployments typically require higher reliability, longer device lifespans, and more rigorous security than consumer applications.